Журнальный клуб Интелрос » Joint Force Quarterly » №81, 2016
Dr. Richard E. Berkebile is an Assistant Professor in the Department of Joint, Interagency, and Multinational Operations at the Command and General Staff College, Fort Leavenworth, Kansas.
One of the prime objectives of an adversary is to inflict damage on the joint force. With thinking enemies, vulnerability is an inescapable characteristic of conflict, and every joint force will have vulnerabilities. Contemporary threats transcend space far easier than in the past, and operational protection is not confined to lethal threats to formations located in hostile environments overseas. With modern technology, even individualServicemembers can be targeted directly or indirectly through families or communities and by both lethal and nonlethal means. For example, in August 2015 the Islamic State of Iraq and the Levant published the names, photographs, and addresses of 100 U.S. military personnel and encouraged sympathetic individuals to attack them.1

Seaman stands force protection watch in 7-meter rigid hull inflatable boat while amphibious transport dock ship USS Ponce (LPD 15) gets under way after port visit at Seychelles, November 2010 (U.S. Navy/Nathanael Miller)
Joint doctrine conceives protection in two contexts.2 The first context is as a function focused on preserving the joint force’s fighting potential.3 The second is as a mission to protect civilians.4 Joint Publication (JP) 1-0, Doctrine for the Armed Forces of the United States, states that military operations are most effective when integrated and synchronized in time, space, and purpose.5 This article adapts that insight and analyzes the function and mission contexts of protection through the lenses of purpose, space, force, and time.
What Is Protection?
JP 3-0, Joint Operations, defines protection as the “preservation of the effectiveness and survivability of mission-related military and nonmilitary personnel, equipment, facilities, information, and infrastructure deployed or located within or outside the boundaries of a given operational area.”6 This definition addresses the protection function in terms of purpose, location in space, and objects to be protected. Protecting denotes shielding from injury, destruction, or detrimental effect, while protection is the act of protecting or sheltering from danger or harm.
Protection does not accomplish political or military objectives in its own right. It is defensive in nature, but not passive. It differs from defending, but the concepts are related and not mutually exclusive. In a military context, defensive operations are more often associated with the maneuver function and more fully engage the fires function. In traditional warfare, protection tends to occur at a greater distance from the source of the threat than defense.
Purpose
Protection’s military application is broad. At a fundamental level, militaries exist to protect the state. For this article, however, the vast remit of protection is narrowed to two purposes. The first is protecting the joint force itself.7 To be useful, the joint force must survive as an effective fighting force. In other words, the joint force is the essential object of protection. This is implied in the functional focus on preserving the joint force’s fighting potential.8
The other purpose is to protect nonforce elements, that is, anything that is not part of the joint force. Nonforce element is an author-invented term aggregating mission-related nonmilitary personnel, equipment, facilities, information, and infrastructure for brevity.9 These nonforce elements are contingent objects of protection. When protective capabilities are scarce, nonforce elements must be prioritized based on their value to the campaign or achieving strategic outcomes. The joint force is the primary military means to provide protection for both nonforce elements and itself. The reverse is generally not true.
JP 3-0 does not explain the phrasing “conserving the joint force’s fighting potential” as opposed to just “conserving the joint force.”10 Conjecturally, this wording could refer to preservation of fighting potential as the outcome of successfully protecting the joint force.11 More likely, however, it references the need to prioritize protection capabilities so violence can be “applied at the decisive time and place.”12 The difference between the joint force itself and its fighting potential is nuanced. Contextually, some parts of the joint force’s fighting potential will matter more. While no commander wants to suffer loss of any kind, the key is to be able to absorb the enemy’s blows while continuing to prosecute the campaign. A vital object of protection is the friendly operational center of gravity or its constituent critical requirements. Assuming that some part of the joint force is the center of gravity, sufficient damage to it would, by definition, severely impede or entirely derail the achieving of campaign objectives.13
JP 3-0 is instructive, stating that “as the JFC’s [joint force commander’s] mission requires, the protection function also extends beyond force protection to encompass protection of U.S. noncombatants; the forces, systems, and civil infrastructure of friendly nations; and interorganizational partners.”14 Note that broadening beyond the force is formission requirements and necessarily includes nonforce elements. Protecting nonforce elements may be the object of the mission or simply a necessary factor for successfully completing another mission. JP 3-16, Multinational Operations, does not include the American noncombatant caveat and allows for broader protection of any noncombatant.15
The defense of nonforce elements should not degrade or divert the capabilities needed to sufficiently protect the joint force. Sufficient protection is not necessarily maximum protection. The commander must balance acceptable risk to the force and risk to the mission. The second consideration is not between the joint force and nonforce elements, but among the nonforce elements themselves. Their value is determined through analysis of the operational environment. In short, the greater the contribution to campaign success or strategic outcomes, the more valuable the element is.
Conversely, accomplishing the mission inherently involves risking at least part of the force. For example, during stability operations, interaction with people may encourage them to have confidence in their security and the legitimacy and competence of their own government primarily and an intervening power secondarily. Restricting the joint force to self-protecting operating bases is unlikely to accomplish this.
An example from the 1994 Operation Uphold Democracy in Haiti illustrates this point. Major General David C. Meade, USA, commander of Joint Task Force 190 (JTF 190) and the 10th Mountain Division, took a conservative approach, keeping Soldiers in protective equipment and confining them to operating bases. Brigadier General Richard W. Potter, Jr., USA, commander of Special Operations Forces/Task Force Raleigh (TF Raleigh) placed his forces in soft caps and engaged with the local population.16 In the short term, TF Raleigh was less protected. In the long term, however, it may have gained better situational awareness and developed intelligence sources, leaving its members better protected. In contrast, JTF 190 may have been ignorant of developing threats or ceded enemies an opportunity to recruit in uncontested civil areas. Alternatively, Major General Meade, fresh from his experience in Somalia, may have considered a moderately successful enemy attack a risk to the entire operation.
In short, factors that influence the wisdom of extending protection beyond the joint force could include:

Seaman from Riverine Squadron 1 observes members of Royal Thai navy riverine squadron conduct force protection exercise on fishing vessel and patrol boat during Cooperation Afloat Readiness and Training Thailand 2011, Sattahip, Thailand, May 2011 (U.S. Navy/Katerine Noll)
Protection’s Space
A common reason for protection failures is an attack on an unanticipated location or domain. It is all too easy for cracks to appear due to poor spatial analysis or faulty assignment of responsibilities. The totality of the protection problem requires disaggregating space to reveal intricate relationships among environments, areas, and domains.
JP 3-0 conceives of military operations as inhabiting a world consisting of environments, areas, domains, dimensions, and systems. Doctrine employs operational environment (OE) to describe the “composite of the conditions, circumstances, and influences that affect the employment of capabilities and bear on the decisions of the commander.”18 Operational area (OA) is an overarching and rather elastic term used to describe several different military spatial delineations of physical areas.19 To conceive of protection across space, I considered environments to include at least some element of physical area. (Unpersuaded readers may substitute area of interest for operational environment for the remainder of the article.)
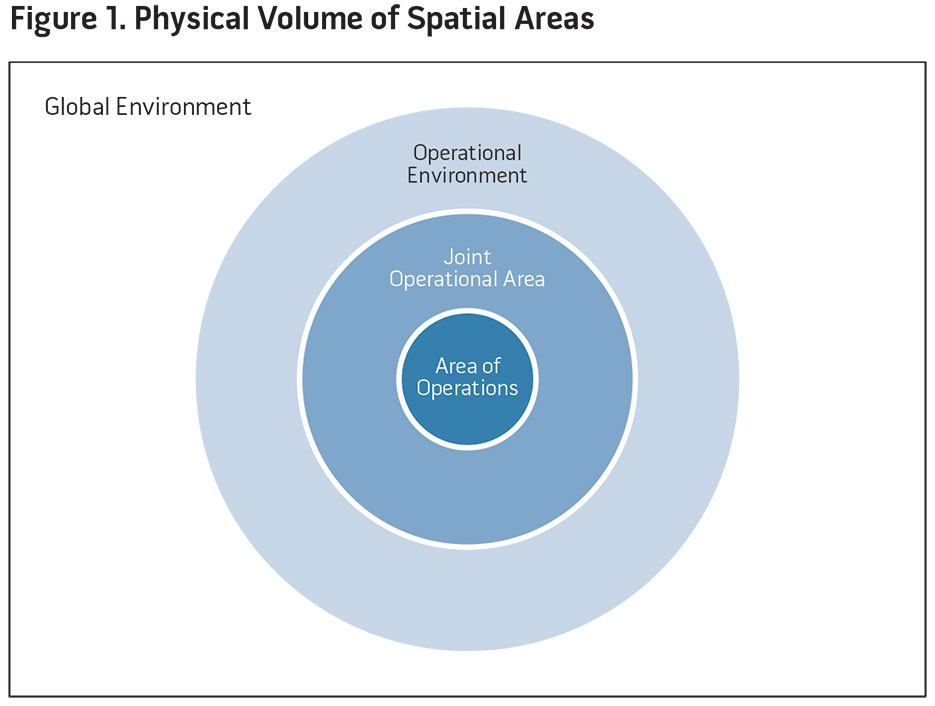
Conceptually, the joint force operational environment could be synonymous with the global environment. Indeed, the information environment and cyberspace domain are specifically described that way in JP 3-0.20 The joint force is likely to focus on an OE that is a subset of the global environment. Joint operational areas (JOAs), or the spaces in which joint forces conduct operations, could likewise be synonymous with the operational environment. However, they are more likely to be lesser included physical spaces within it. Areas of operation are subdivisions of JOAs assigned to land and maritime components.21 Figure 1 is a conceptual depiction of the physical volume of spatial areas.
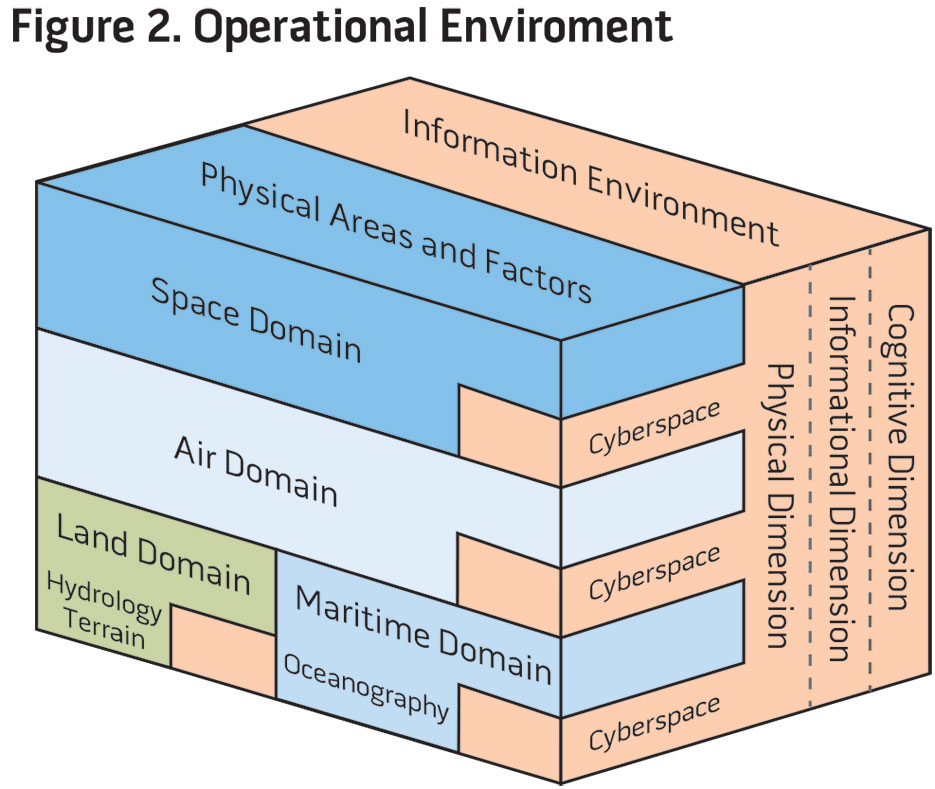
Planning protection requires further division of environments and areas into domains, the venues for fighting. JP 3-0 divides space into physical air, land, maritime, and space domains and the information environment.22 The information environment requires further elaboration. It contains its own cyberspace domain and physical, information, and cognitive dimensions.23 Figure 2 is a modified version of an operational environment graphic found in JP 2-01.3, Joint Intelligence Preparation of the Operational Environment.24
If one accepts that the OE is a subset of the global environment, then the information environment transcends the operational environment and is not contained by the OE, as may be inferred from figure 2. If one further overlays the joint force’s requirement for protection across space, the depiction resembles figure 3.

Protection’s Force
Forces execute protection. These forces may include the joint force, residual military forces, or certain civilian governmental, commercial, or private entities. The technologies of the information age have compressed space and time intervals between battlefields and political outcomes. In particular, the joint force may be vulnerable in the information environment and the cyber and space domains well beyond the JOA. As technology compresses space, the joint force becomes increasingly dependent on protection capabilities provided through coordination and cooperation rather than organic assets. Here, the question concerns the joint force and its generalized application of protection capabilities.
Capabilities. Protection can be implemented in four primary ways: active defense, passive defense, emergency management and response, and fratricide prevention.25 JP 3-0 operationalized these in terms of tasks and key considerations—essentially expanded descriptions of the tasks. Each of these ways or tasks implies a need for a corresponding capability to accomplish it. (Doctrine does not align tasks and key considerations with any particular way.) Discounting the inevitable overlap, I reworded protection tasks and aligned them with the four ways.26 Two key considerations that were not obviously restated tasks were included. The personnel recovery task did not align with any of the specified ways:
A close examination of the ways, tasks, and key considerations disclosed five important points. First, JP 3-0 suggests that, at least at the operational level, the scope of the operation is only marginally related to the range of necessary tasks.29 This implies that a full range of protection capabilities should be both considered and available for any contingency.
Second, domains are not necessarily bounded. Some protection capabilities are executed in more than one domain, while others are executed in a single domain but provide protection in several. Both joint force and national protection capabilities and responsibilities may cross the JOA boundary. Lastly, as conditioned by proximity, protection need not secure force and nonforce elements in isolation.
The following example illustrates protection’s spatial variability. Area missile defense protects targets in land, maritime, air, and possibly space and cyber domains. As headquarters, ports, air bases, and transportation hubs are often near urban areas, missile defense can protect both the joint force and nonforce elements, albeit at varying levels of efficiency. If the protection priority is high enough, the commander may divert capabilities from other missions. Military forces of higher echelons may also perform the mission. During the Southwest Asia campaign of 1990–1991, of which Operations Desert Shield and Desert Storm were a part, U.S. Patriot missile batteries were sent to defend Israeli nonforce elements, and air missions were retasked to perform Scud suppression even though Israel was neither a party to the conflict nor located in the JOA.30
Third, task descriptions are oriented toward the operational level of war. Only one, critical infrastructure protection, is clearly described at both an operational and a strategic level.31 A review of the January 2015 Universal Joint Task List reveals that a form of the protection tasks is maintained across all levels of war.32
Fourth, JP 3-0 views emergency management and response narrowly in terms of accompanying damage from accidents, health threats, and natural disasters.33 Emergency management and response should be expanded to include reaction to intentional hostile action. For example, I categorized CBRN consequence management, which is likely the result of deliberate hostility, under emergency management and response. Additionally, recovery actions in the aftermath of a conventional attack could easily be included in a redefined emergency management plan. This does not imply a lack of capability to perform emergency management and response but could achieve the same effect by creating a seam in conceiving and planning protection.
Finally, JP 3-0 is oriented toward external threats. Protection, however, also has a vital internal aspect. While fratricide prevention is internally focused, it is directed solely against unintentional harm. Contemporary technology and, arguably, political culture increase internal vulnerability to intentional or even ambient subversion. Stated differently, “we” could be a credible enemy requiring a corresponding protection task and capability. JP 3-10, Joint Security Operations in Theater, marks considerable progress toward addressing insider threats. While it specifically addresses such threats, it is not overarching protection doctrine. The Army supplements joint protection tasks with two additional internally focused ones: employing safety techniques and conducting law and order operations.34
Counteracting internal threats requires corresponding capabilities. Some could be capabilities in the traditional sense such as technical means to detect espionage. The key to internal force assurance, however, may lie buried within the information environment’s informational and cognitive dimensions. Protection in these dimensions could have elements of technical capabilities, but it is more likely to require human solutions.
Vulnerabilities. Borrowing from Frederick II of Prussia, “he who defends everything defends nothing.” The joint force has considerably more valuable military and nonforce assets to protect than just the friendly center of gravity. Protection prioritization across domains and the information environment will be key.
In the context of the air and missile defense task, JP 3-01, Countering Air and Missile Threats, directs the assembling of a critical asset list (CAL) based on three criteria: the potential target’s mission criticality, its vulnerability (a determination based on susceptibility to and recoverability from attack), and the credibility of the threat.35 A defended asset list (DAL) is then derived by the prioritized assignment of available air and missile defense capabilities.36 JP 3-31, Command and Control for Joint Land Operations, suggests a similar method be used for the cyberspace domain.37 The method is sensible as far as it goes. It simply needs to be applied across all domains. In other words, all domain and environment vulnerabilities require a centralized CAL and DAL process.

CBRN defense specialist Marine radios team during joint-training exercise between III Marine Expeditionary Forces CBRNE Ordnance Disposal units at Central Training Area, Camp Hansen, Okinawa, January 2016 (U.S. Marine Corps/Kelsey M. Dornfeld)
Protection’s Time
Protection never rests. Or at least it should never rest. But duration is only one aspect of time, and labeling protection timeless does not end the discussion. Given vulnerabilities and capability scarcity, operational protection requires analysis of time’s simultaneity and timing aspects. These aspects are influenced by level of war and by the phasing of operational campaigns. Although this article largely examines only operational war, the protection function spans all levels. Analyzing time requires a brief diversion into strategic and tactical protection.
Strategic Protection. The need for strategic protection is continuous. Milan Vego posits that strategic protection is about sources of power.38 National power may be considered the state’s ability to exercise “control over the minds and actions of other” people or states.39 Sources of power, then, are intrinsically valuable entities whose protection is in the national interest. Their vulnerability is elevated or demoted by current global tensions, military campaigns, or enemy capabilities. Even if negligible in a particular campaign, sources of power are always at risk from potential enemies. Protection from strategic surprise is generally the result of long-term planning and is implemented at the national level. In a broader sense, strategic protection is a necessary component of strategic deterrence.
For example, the loss or sustained disruption of major urban centers, critical economic institutions or infrastructure, governance institutions, strategic military capabilities, or vital communications infrastructure would seriously affect the national psyche or quality of life and, conceivably, national survival. Sources of power would generally be outside the OE, except for homeland or U.S. Northern Command (USNORTHCOM) area of responsibility operations,40 and the joint force would not be responsible for their protection. For example, USNORTHCOM orchestrates ballistic missile defense of the homeland. With current technology and likely threats, protection simultaneity and timing coordination is muted for strategic protection.
Tactical Protection. Tactical protection is local and largely of a self-help nature. According to Vego, it is unit and platform focused.41 Tactical protection is an inherent command responsibility for all organizations. Even though acceptable risk may vary considerably, tactical protection should occur regardless of location in space. Tactical protection is not bounded by time, and its planning horizons are near term. Risk is higher during times of conflict but is never nonexistent. For example, attacks in the information environment and cyber domain are daily occurrences, although some international actors may be holding their most damaging capabilities in abeyance. Tactical protection is intrinsic, but units do not have equal capability to provide it across domains. Some protection capabilities must be aggregated at higher levels. For example, most units would be incapable of providing their own air or space defense.
Operational Protection. For operational protection, simultaneity and timing are essential aspects of time. Dale C. Eikmeier points out the offensive features of simultaneity: “multiple actions at the same time and appropriately synchronized pressure on multiple points . . . of an enemy’s systems and/or CoG [center of gravity].”42 Protection’s simultaneity is the flip side of the coin; it is the prioritization and synchronization of capabilities to defend friendly critical vulnerabilities and decisive points across vulnerable domains and the information environment. In other words, skilled enemies are likely to plan multidomain attacks against the joint force.
Eikmeier also notes, “Timing refers to when to apply specific capabilities.”43 Protection priorities and requirements are dynamic. As campaigns unfold and the global environment impinges on the operational environment, planners must anticipate and react to change. Enemy capabilities will strengthen or weaken, and the enemy will adapt. The main effort and relative importance of friendly forces will likewise change. Variations will not affect all domains equally. Effective protection requires constant attention and adjustment over time.
Phasing is an operational tool used to synchronize and sequence timing during campaigns.44 Vego observes that there is no operational level of war without active operations45 and that JTFs are only temporary organizations, not permanent. This aligns Phase 0, shaping activities, with combatant commands at the strategic level of war. Even so, operational protection in some form begins in Phase 0. Generally, the onset of military operations is not a total surprise. Tensions build openly in the information environment, leading to anticipatory behavior by both friendly and enemy forces. The operational impact of a moderately successful Phase 0 attack escalates for specialized high-demand, low-density assets and as the size of extant military forces, particularly potential joint force headquarters, shrinks.
Protection timing can be roughly illustrated using the protection doctrine’s dominant narrative, in which the joint force deploys to a host nation that is threatened by or suffering depredations from a common enemy:
Protection is a vital function that transcends space and time. Modern technology is increasing the reach of threats, allowing them to cross more domains in much less time. The defense community needs to think deeply about the concept of protection. A purpose, space, force, and time framework is a useful supplement to the function and mission contexts of protection doctrine. Operational protection requires comprehensive planning across operational areas, domains, and phases. It does not occur in isolation. Coordination with appropriate headquarters beyond the OE and tactical forces within the OE is necessary. JFQ

Airmen work in Global Strategic Warning and Space Surveillance System Center at Cheyenne Mountain Air Force Station, Colorado, September 2014 (U.S. Air Force/Krystal Ardrey)
Notes
1 Tom Wilson, “ISIS Releases Hit List of 100 American Military Personnel,” New York Post, March 22, 2015.
2 I thank an anonymous reviewer for this insight. Any mistakes interpreting or applying the insight are my own.
3 Joint Publication (JP) 3-0, Joint Operations (Washington, DC: The Joint Staff, August 11, 2011), III-29, is the overarching publication. Related publications concentrating on specific force preservation tasks include JP 3-50,Personnel Recovery (Washington, DC: The Joint Staff, December 20, 2011); JP 3-10, Joint Security Operations in Theater (Washington, DC: The Joint Staff, November 13, 2014); JP 3-15.1, Counter-Improvised Explosive Device Operations (Washington, DC: The Joint Staff, January 9, 2012); JP 3-13.3, Operations Security (Washington, DC: The Joint Staff, January 4, 2012); JP 3-01, Countering Air and Missile Threats (Washington, DC: The Joint Staff, March 23, 2012); JP 3-41, Chemical, Biological, Radiological, and Nuclear Consequence Management(Washington, DC: The Joint Staff, June 21, 2012); JP 3-07.2, Antiterrorism (Washington, DC: The Joint Staff, November 24, 2010); JP 4-02, Health Service Support (Washington, DC: The Joint Staff, July 26, 2012).
4 JP 3-07.3, Peace Operations (Washington, DC: The Joint Staff, August 1, 2012); JP 3-07, Stability Operations(Washington, DC: The Joint Staff, September 29, 2011); JP 3-22, Foreign Internal Defense (Washington, DC: The Joint Staff, July 12, 2010); JP 3-24, Counterinsurgency (Washington, DC: The Joint Staff, November 22, 2013); JP 3-28, Defense Support of Civil Authorities (Washington, DC: The Joint Staff, February 19, 2013); JP 3-29, Foreign Humanitarian Assistance (Washington, DC: The Joint Staff, January 3, 2014); JP 3-68, Noncombatant Evacuation Operations (Washington, DC: The Joint Staff, January 22, 2007).
5 JP 1, Doctrine for the Armed Forces of the United States (Washington, DC: The Joint Staff, March 25, 2013), I-20; JP 3-0, I-1.
6 JP 3-0 also defines protection in a space and shipping context, but including them here would not contribute to the overall thesis of the article.
7 In the abstract, the joint force could be synonymous with the entire national military establishment. It is more likely a subset of all military forces organized in a joint task force.
8 JP 3-0, III-29; Protection Joint Functional Concept: Version 1.0 (Washington, DC: Department of Defense, June 3, 2004), 7.
9 It also allows for the possibility that personnel, equipment, facilities, information, and infrastructure may not be an exhaustive list.
10 See Universal Joint Task List, available at <www.dtic.mil/doctrine/training/ujtl_tasks.pdf>.
11 Protection Joint Functional Concept.
12 JP 3-0, III-30.
13 JP 5-0, Joint Operation Planning (Washington, DC: The Joint Staff, August 11, 2011), III-22–23.
14 JP 3-0, III-29.
15 JP 3-16, Multinational Operations (Washington, DC: The Joint Staff, July 16, 2013), III-11.
16 Walter E. Kretchik, Robert F. Baumann, and John T. Fishel, Invasion, Intervention, “Intervasion”: A Concise History of the U.S. Army in Operation Uphold Democracy (Fort Leavenworth, KS: U.S. Army Command and General Staff College Press, 1998).
17 Jim O’Sullivan and Tom Madigan, “Mullen: Qaddafi Could Still Stay in Power,” National Journal, March 20, 2011.
18 JP 3-0.
19 Ibid., IV-1.
20 Ibid., IV-2.
21 Ibid., IV-13.
22 Milan Vego, Joint Operational Warfare: Theory and Practice (Newport, RI: U.S. Naval War College Press, 2009), III-65–72. Vego presents an excellent discussion of whether the information environment is an additional element of the time, space, and purpose construct.
23 JP 2-01.3, Joint Intelligence Preparation of the Operational Environment (Washington, DC: The Joint Staff, June 16, 2009), II-27.
24 JP 2-01.3, Joint Intelligence Preparation of the Operational Environment (Washington, DC: The Joint Staff, May 21, 2014), I-3.
25 JP 3-0.
26 Ibid., III-30.
27 Ibid., III-34.
28 Ibid.
29 Ibid., III-30.
30 The 1993 version of JP 3-0 uses the term joint operations area. It is unclear if the term was used in 1990–1991.
31 JP 3-0, III-34.
32 Universal Joint Task List.
33 JP 3-0, III-29.
34 Army Doctrine Reference Publication 3-37, Protection (Washington, DC: Headquarters Department of the Army, August 2012), 1–3.
35 JP 3-68, III-20.
36 Ibid., III-21.
37 JP 3-31, Command and Control for Joint Land Operations (Washington, DC: The Joint Staff, February 24, 2014), II-21.
38 Adopted from Vego, VIII-95.
39 Hans Morgenthau, Politics Among Nations: The Struggle for Power and Peace, 4th ed. (Caledonia: McGraw-Hill, 1967), 26.
40 Doctrine defines homeland as the United States, its territories, and the surrounding waters and airspace (JP 3-16, I-2). This includes Guam. For this article, references to the homeland exclude Guam but include Puerto Rico and the Virgin Islands. Hawaii is part of the homeland but is in the U.S. Pacific Command area of operation (except for missile defense).
41 Vego, VIII-96–97.
42 Dale C. Eikmeier, “From Operational Art to Operational Plans: A Joint Planning Primer,” Fort Leavenworth, KS, 2012, 44; JP 3-0.
43 Eikmeier, 45.
44 JP 3-0, III-36.
45 Vego, VIII-95.
46 Field Manual 3-24/Marine Corps Warfighting Publication 3-33.5, Insurgencies and Countering Insurgencies(Washington, DC: Headquarters Department of the Army, May 13, 2014).